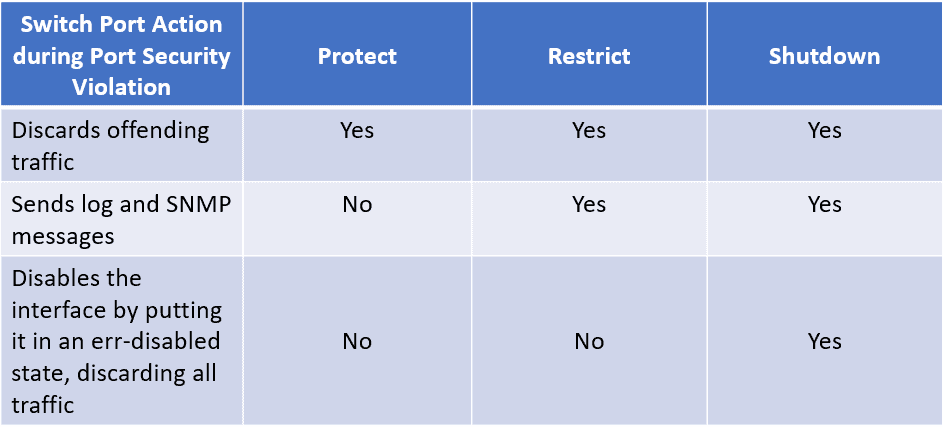
Switch Security: Management and Implementation (2.2) > Cisco Networking Academy's Introduction to Basic Switching Concepts and Configuration | Cisco Press
Switch Security: Management and Implementation (2.2) > Cisco Networking Academy's Introduction to Basic Switching Concepts and Configuration | Cisco Press




![Configuring Port Security [Cisco Nexus 5000 Series Switches] - Cisco Systems Configuring Port Security [Cisco Nexus 5000 Series Switches] - Cisco Systems](https://www.cisco.com/en/US/i/000001-100000/95001-100000/99001-100000/99301.jpg)